OpenAI introduced Daybreak on May 11, a new cybersecurity initiative designed to help find, verify, and fix software vulnerabilities before attackers can exploit them.
The company describes its approach as making software “resilient by design” and moving security early in the build cycle through AI-assisted code reviews, threat modeling, patch validation, and dependency analysis.
In the case of cryptocurrencies, the urgency is clear, as software failures can lead to immediate capital loss within a single block.
The standard pattern in the cryptocurrency industry is reactive, with pre-launch audits, post-deployment monitoring, fund transfer actions, methodological postmortems, vulnerability patching, redemption negotiations, and governance discussions.
This model has the weakness that bugs are only discovered after the capital has been relocated. The window between deployment and exploitation is when the risk is highest and defenses are weakest.
TRM Labs’ 2026 Crypto Crime Report shows that illegal actors stole $2.87 billion in approximately 150 hacks and exploits in 2025. Infrastructure attacks via compromised keys, wallet infrastructure, privileged access, front-end surfaces, and control planes accounted for $2.2 billion of this.
Code exploits were the category most audits directly addressed, accounting for $350 million (12.1%).
Hacken’s first quarter data confirms that audit-centric security has real limits, as Web3 lost $482 million in 44 incidents in the first quarter. Six of these incidents involved audited protocols, including one that had undergone 18 separate audits.
The $282 million theft involved no code exploits and allowed the attackers to completely bypass the contract layer and compromise the operational and social infrastructure around it.
CertiK’s latest Wrench Attacks report notes that 34 incidents of physical force were confirmed globally between January and April 2026, an increase of 41% compared to the same period in 2025, resulting in an estimated loss of approximately $101 million over that four-month period.
On this trajectory, CertiK estimates that 2026 could end with around 130 incidents. The attack vector could be the person holding the key, the multisig signer, or the engineer with access to the cloud console.
Together, the three datasets describe threats that have moved far beyond smart contracts.
Cryptocurrency requires “resilient design”
Daybreak logic applies to cryptocurrencies and refers to the security posture that is continuously enforced throughout the lifecycle of the protocol.
OpenAI describes AI that can reason through your codebase, identify subtle vulnerabilities, verify that a fix actually solves the underlying problem, and bring that functionality into your daily build and deployment workflows as an ongoing feature.
For cryptocurrencies, this translates into specific operational requirements across the full stack where losses are currently concentrated.
AI-assisted secure code reviews performed before and throughout deployment detect logic errors, access control gaps, and unsafe assumptions before they reach mainnet. Continuous threat modeling across protocol upgrades to assess how each architectural update, oracle dependency, bridge design, or governance mechanism opens up new attack surfaces.
Dependency and Oracle risk analysis flags when third-party integrations weaken the security model of the protocols that depend on them.
Patch validation before governance runs ensures that the proposed fixes eliminate vulnerabilities and that the fixes themselves persist under hostile conditions.
Privileged access reviews of multisig, signers, front-end deployments, and storage systems are performed regularly as part of standard operating procedures. Monitoring for anomalous behavior before funds leave can reduce the time between detection and response.
Security Features What to Check Why Encryption AI-Assisted Secure Code Reviews Matter Contract logic, access controls, unsafe assumptions, and upgrade-related bugs before and during deployment Helps discover exploitable flaws before they reach mainnet, where failure can result in immediate capital loss Continuous threat modeling How protocol upgrades, architectural changes, governance mechanisms, oracle links, and bridge design create new attack surfaces Maintain security as the protocol evolves, rather than treating risks as fixed at launch Dependency and oracle risk analysis Whether third-party libraries, oracle providers, middleware, or bridge components are undermining the protocol’s security model Many critical failures now originate from the broader stack around the contract, rather than from the contract itself Patch validation before governance runs Does the proposed fix actually address the underlying vulnerability and remain secure under hostile conditions? Prevent governance from approving patches that appear correct but leave exploit paths open or create new ones. Review of privileged access. Multisig, signers, custody systems, administrative keys, cloud console access, and front-end deployment privileges. Infrastructure attacks increasingly target people and systems with the power to move funds or change protocol behavior. Pre-exfiltration monitoring. Abnormal transaction patterns, suspicious signer behavior, unusual front-end changes, and withdrawal anomalies Reduce the time between detection and response, giving your team the opportunity to intervene before losses escalate.
Cryptographic protocols with extensive audit records continue to leave front-end deployments unmonitored or multisig misconfigured, leaving operational blind spots with some of the biggest losses of 2025.
OpenAI said malicious parties can exploit expanded cyber capabilities, and Daybreak combines its defensive tools with verification, scoped access, safeguards, abuse monitoring, and stronger account controls.
The same AI capabilities that help defenders review code, validate patches, and model threats can help attackers accelerate phishing, generate convincing fake front ends, clone legitimate protocols, analyze dependency chains for exploitable weaknesses, and extend social engineering across admins, signers, and support channels.
Hacken’s data ranks phishing as the primary attack vector, and CertiK’s physical coercion data shows that attackers are directly targeting people. Both categories include social and operational operations, and AI operates at scale in both.
Two achievements for cryptocurrency security
The bull case is that “resilience by design” becomes the competitive standard.
Protocols will begin to treat continuous code reviews, auditing signer policies, dependency checking, front-end integrity monitoring, and validating governance enforcement as standard requirements throughout the protocol lifecycle.
In this model, audit proofs are replaced by a complete operational stack of signers, upgrades, dependencies, and access controls to prove resiliency before execution.
OpenAI’s unique approach, which combines more capable tools with powerful validation and process controls, is an external template in that direction.
According to TRM data, when 76% of losses are caused by infrastructure, the following security standards should be applied there: Protocols that can demonstrate ongoing operational resiliency will be easier to make the case to insurers, regulators, and institutional investors than those that only present a stack of audit certificates.
The bearish note is that AI-assisted security remains in the marketing tier.
The protocol adds AI-powered security language to the documentation, and the underlying operational model remains fixed with pre-launch auditing and post-exploitation post-mortem.
Attackers use the same tools to scale up phishing, clone front ends more quickly, and compromise support channels more convincingly than defenders can improve their workflows.
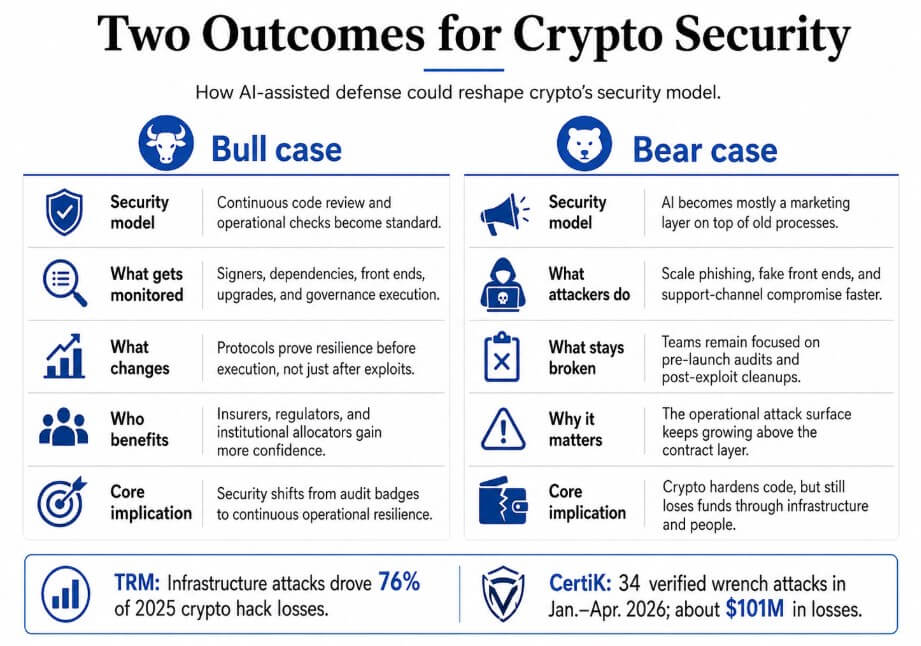
Hacken’s discovery that an attacker stole $282 million without touching a single line of contract code shows that the attack surface extends beyond the contract layer and that the industry’s current security frameworks only cover a portion of it.
The cryptocurrency industry has focused its security model on post-exploit response and point-of-exploitation reviews, and the attack surface extends far beyond that.
OpenAI’s new cybersecurity push article includes lessons for cryptocurrencies. Don’t wait for a hack to appear first on CryptoSlate.